
Display port won't detect with my laptop, tried two different adapters and both don't work. Any suggestions on what to do? : r/oculus
My laptop doesn't have a HDMI port, it has a VGA port. My LED TV doesn't have VGA port, it has HDMI. How can I connect my laptop to my tv? -
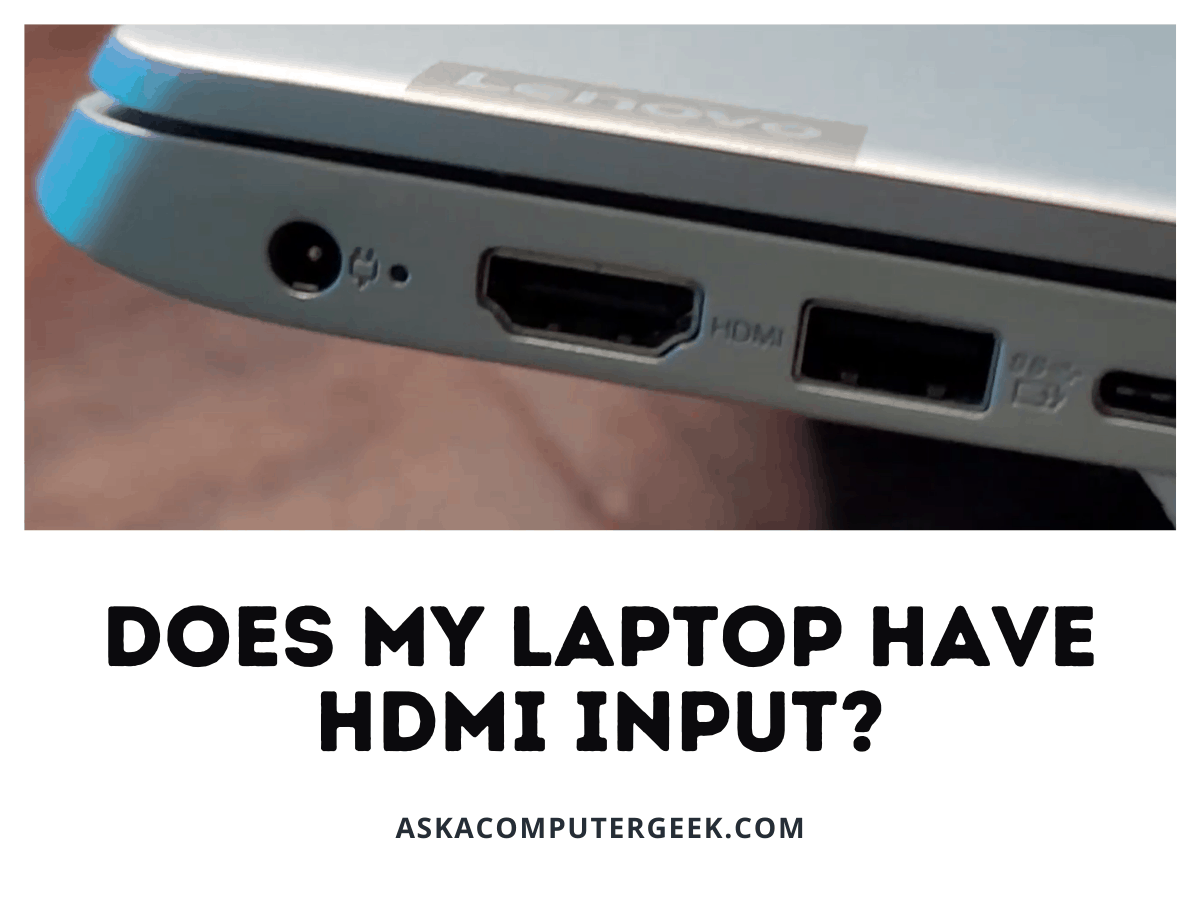
What do I do if I don't have an HDMI port on my Lenovo PC? I have this HDMI to VGA cable but my monitor also has VGA. Did I waste money







![How to Fix HDMI Not Working on Laptop Windows 10? [5 Methods] - YouTube How to Fix HDMI Not Working on Laptop Windows 10? [5 Methods] - YouTube](https://i.ytimg.com/vi/kXTRIDvI8MU/maxresdefault.jpg)









![Tutorial]6 Methods to Fix HDMI Port Not Working on Windows 10 Laptop Tutorial]6 Methods to Fix HDMI Port Not Working on Windows 10 Laptop](https://images.wondershare.com/recoverit/article/2020/03/hdmi-port-not-working-on-laptop-3.jpg)