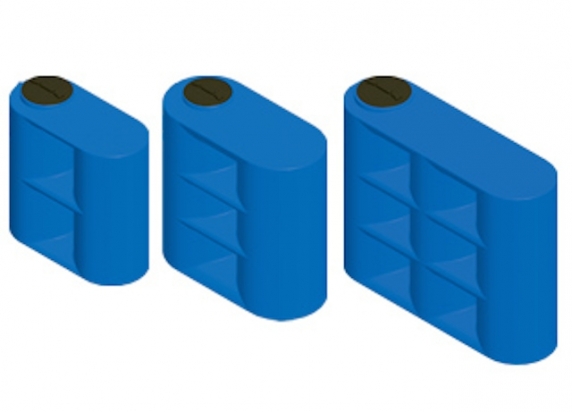
Serbatoio Acqua Cisterna in Polietilene Parallelepipedo Orizzontale da Esterno Giurgola 300 Lt cod. Plro0300

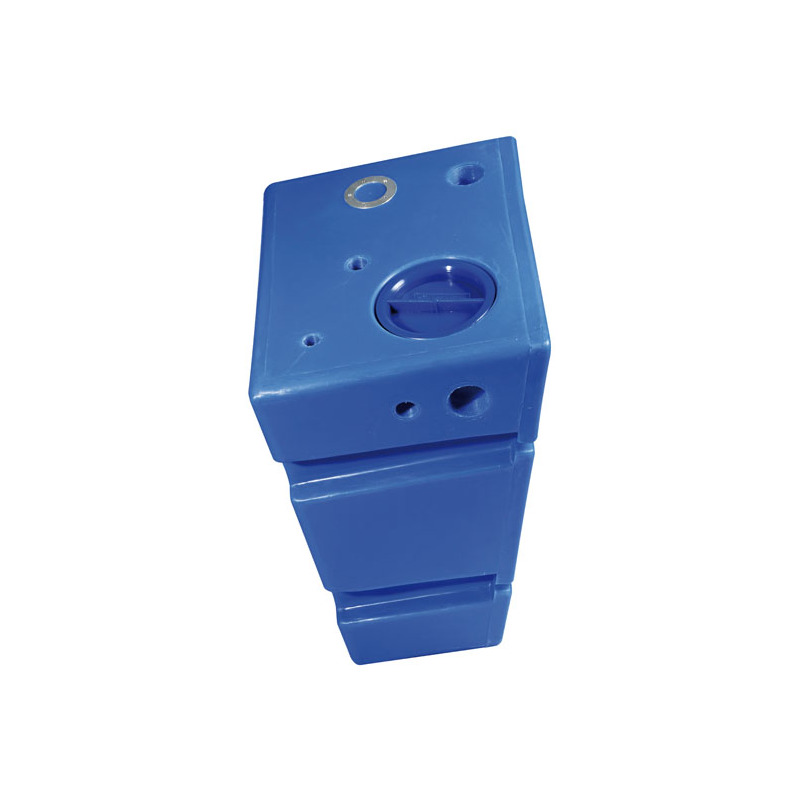
Serbatoio RINFORZATO polietilene 5 mm tipo orizzontale 1000 litri - FORI STAMPATI e FILETTATI acqua potabile alimenti blu cisterna : Amazon.it: Commercio, Industria e Scienza

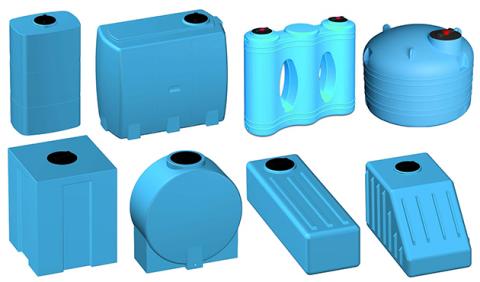
Serbatoi salvaspazio in polietilene per acqua potabile - capienza 800 e 1000 litri Serbatoi cisterne per acqua