Teepee Tenda per Bambini Tenda Indiano con Luci Fatate Tenda da Gioco Portatile Tenda da Gioco Castello Giochi per Bambini per Interni ed Esterni : Amazon.it: Giochi e giocattoli

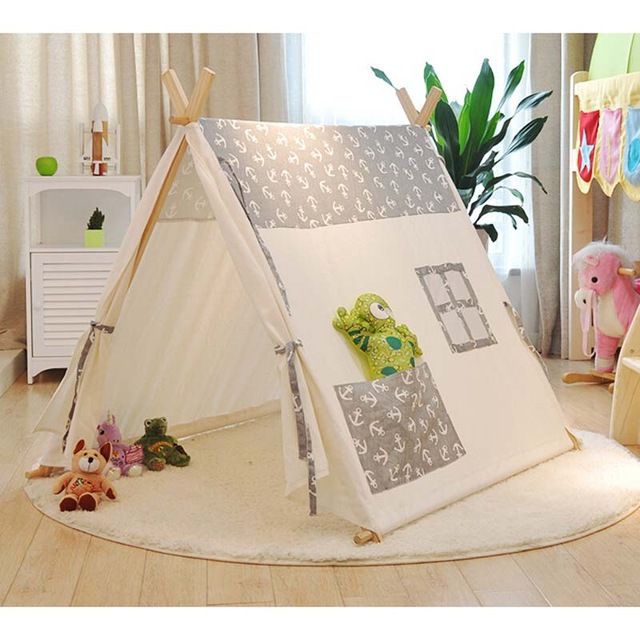
Tenda da castello per bambini casetta da gioco grande tenda per bambini Princess Prince Beach tenda da interno ed esterno casa da gioco giocattoli per ragazze ragazzi|Tende per bambini| - AliExpress

Tenda per Bambini, Tenda Gioco Bambini con Coperta & Fata Luci & Borsa di tela- Tende Indiana Bambini per 3 4 5 6 7 anni… - Giochi e Prodotti per l'Età Evolutiva

ECD GERMANY - Tenda Tipi Per Bambini Da Gioco Cameretta Giocattolo Interno Esterno Tende Blu - ePRICE

Tenda per Bambini, Tenda Gioco Bambini con Coperta & Fata Luci & Borsa di tela- Tende Indiana Bambini per 3 4 5 6 7 anni Bambina & Ragazzi, Tipi, Teepee : Amazon.it: Prima infanzia

Tenda Tipi per bambini - Tenda da gioco Tippi Cameretta per bambini Tenda indiana Teepee Outdoor Indoor Modello 2 con tappetino da gioco e 3 cuscini colore albicocca : Amazon.it: Giochi e giocattoli

Tenda per Bambini, Tenda Gioco Bambini con Coperta & Fata Luci & Borsa di tela- Tende Indiana Bambini per 3 4 5 6 7 anni… - Giochi e Prodotti per l'Età Evolutiva