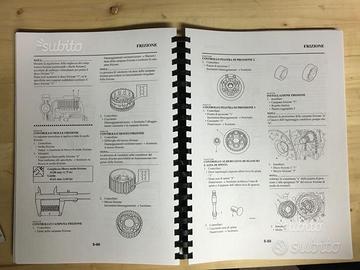
YAMAHA YZF R1 Manuale Di Officina Riparazione 2007 - Workshop Manual Repair IT EUR 4,49 - PicClick IT
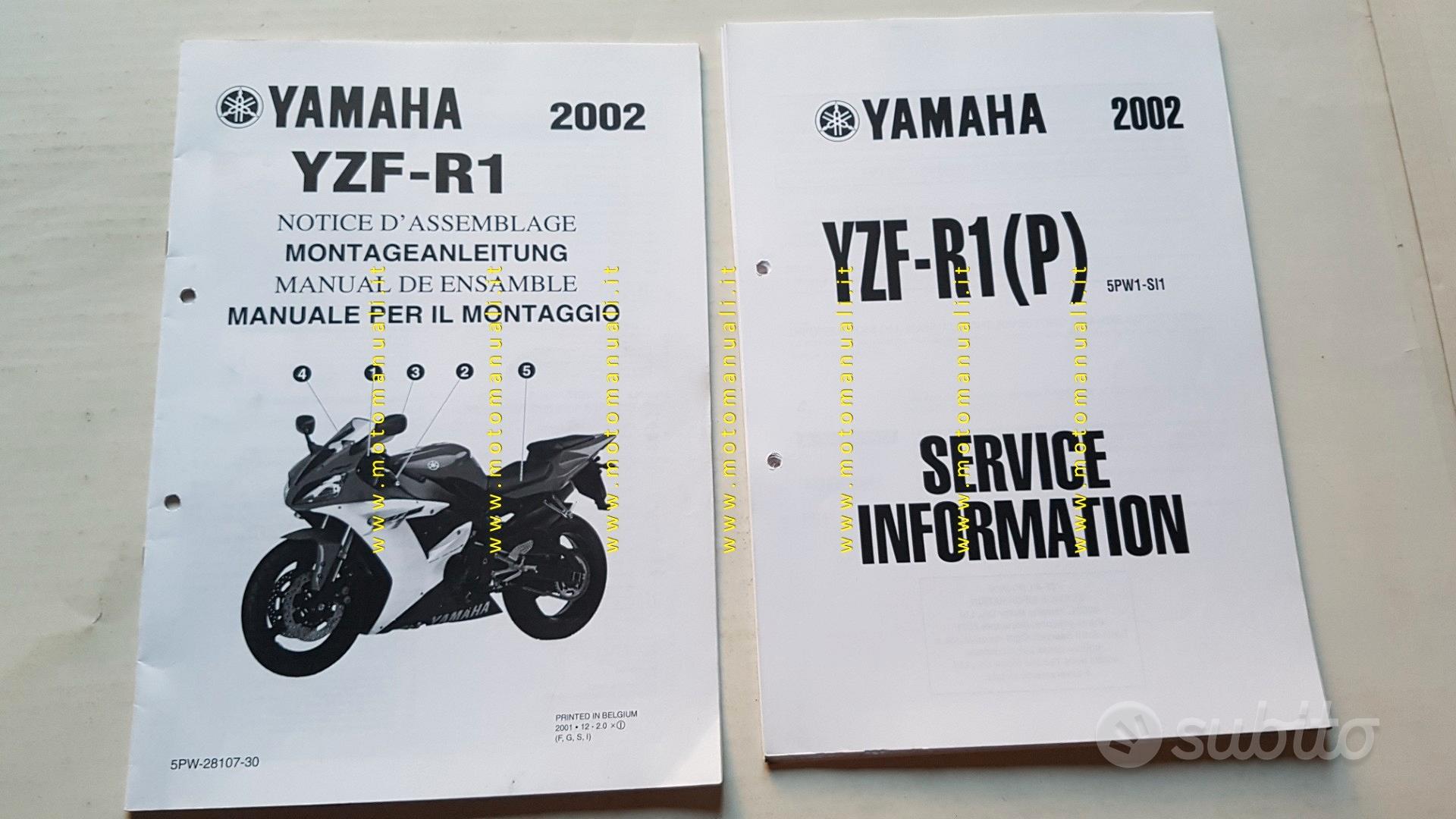
Subito - Motomanuali - Yamaha YZF-R1 2002-3 Service Information manuale o - Accessori Moto In vendita a Milano
YAMAHA DS7 RD250 R5C Rd350 1972 1973 Manuale Officina Workshop Manual Dvd Servic EUR 9,99 - PicClick IT
_yamaha-yzf-r1-service-manual-taller-manuel-reparation-manuale-officina-reparaturanleitung.jpg)
Yamaha YZF-R1, YZF-R1M (2015) - Service Manual Repair Manual - Wiring Diagrams from yamaha r1 service manual download Watch Video - HiFiMov.co

YAMAHA YZF-R1 YZF R1 -YZF R1M Manuale di riparazione assistenza officina 2015 - 2019 su CD EUR 9,57 - PicClick IT
Yamaha YZF R1 2009-2014 (YZF-R1 14B 1KB 2SG) Libretto istruzioni French (14B-28199-F0) | Baboon - World of Motorcycle Parts
_yamaha-yzf-r1-2002-service-manual-manuale-di-officina.jpg)