Bagaglio a Mano 40x20x25 Ryanair - Made In Italy - Borsa da Viaggio - Tracolla e Attacco Trolley - Idrorepellente, Resistente, Ultraleggera e Pieghevole (Blu) : Amazon.it: Moda
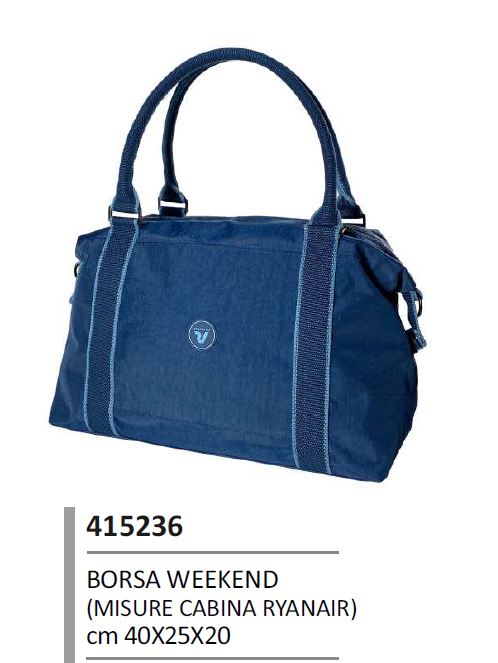
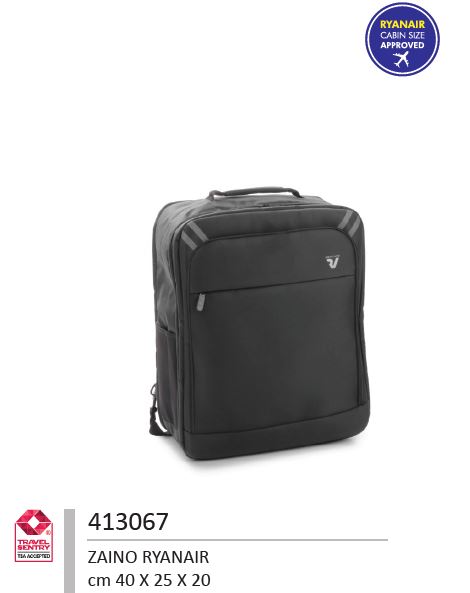
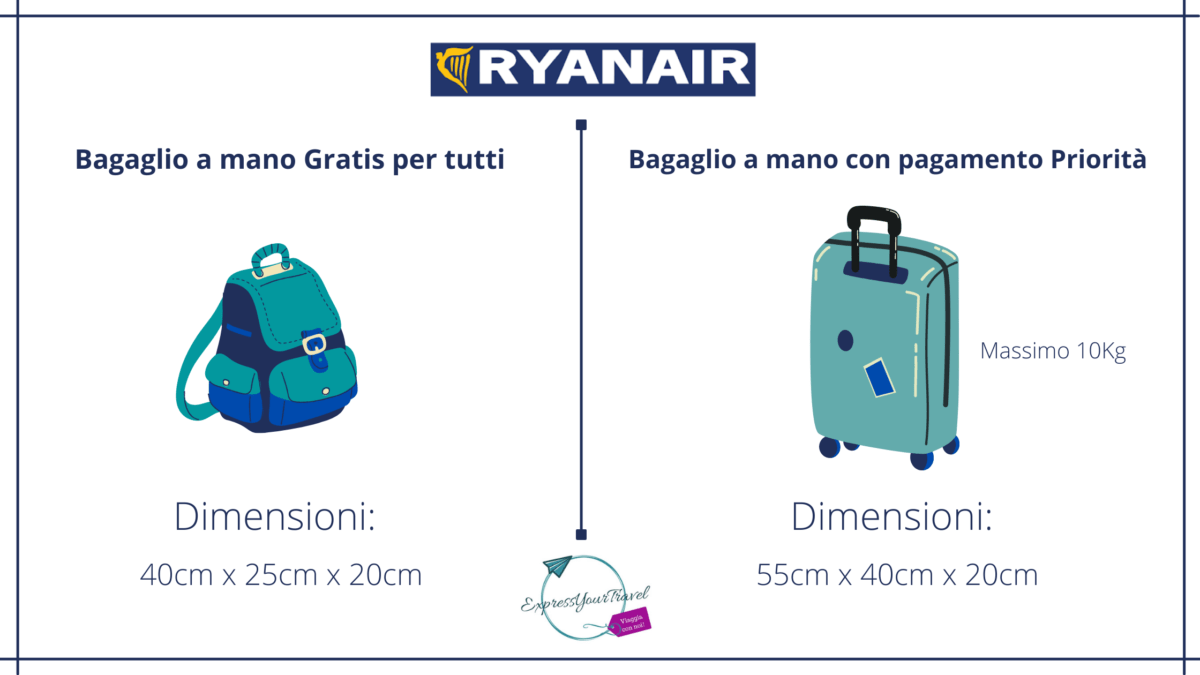
RO415236 Roncato Borsa da Cabina Rolling inisex Misura Bagaglio a Mano GRATUITO RYANAIR - Valigeria e Pelletteria Paul's Bags