Langhaar-Kinderperücke für Mädchen blond , günstige Faschings Accessoires & Zubehör bei Karneval Megastore

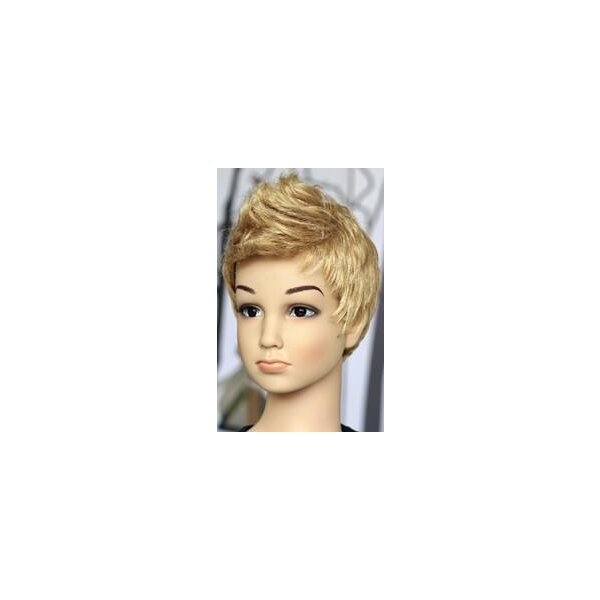
DENING HAIR BELLE MADAME ECHTHAARPERÜCKE - KINDERPERÜCKE GILDA RH 2 · Perücken Luttmann Online-Shop | Pflegeprodukte | Perücken | Haarteile | Zweithaar

Super Saiyjan Vegeta™-Perücke für Kinder Dragon Ball™ blond , günstige Faschings Accessoires & Zubehör bei Karneval Megastore

Kinder-Perücke wellig lang für Halloween und Karneval blond: Accessoires,und günstige Faschingskostüme - Vegaoo