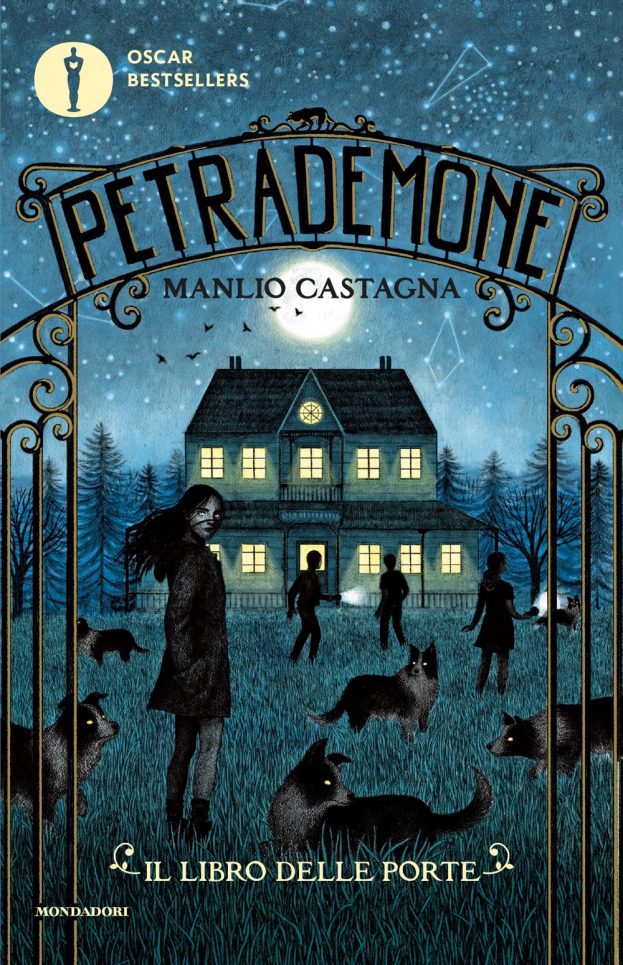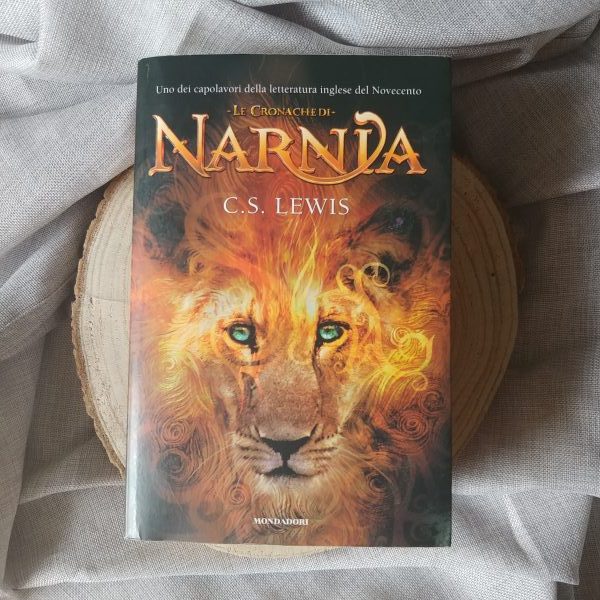
Narrativa di Avventura per bambini e ragazzi Libri, i libri acquistabili on line - 1 - Mondadori Store

Il regno perduto: Un'avventura ricca di colpi di scena, magia e sfide da affrontare. Libri fantasy per bambini e ragazzi 8/12 anni : Rio, Barbara: Amazon.it: Libri